We start step by step with the installation of Ephesoft and Infor SSO Configuration
How to install and configure (SSO) application to be used with Ephesoft Transact and Infor
- Installing Ephesoft
- Creating Self-Signed Certificates Using OpenSSL
- Configure Infor SSO
Installing Ephesoft
Download Ephesoft
Before installation: verify that you have a license for Ephesoft Transact
Log onto the Windows system on which Ephesoft Transact is to be installed, and perform the following tasks to prepare Windows for installation:
- Disable (turn off) the user access control (UAC).
From the Windows Start menu, search for User Access Control or UAC. Windows displays the link for this page from the Control Panel. Click this link to display the page.
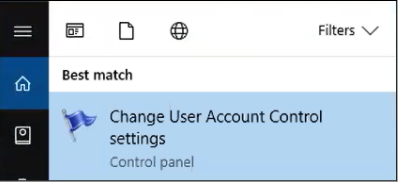
The User Account Control Settings screen appears.
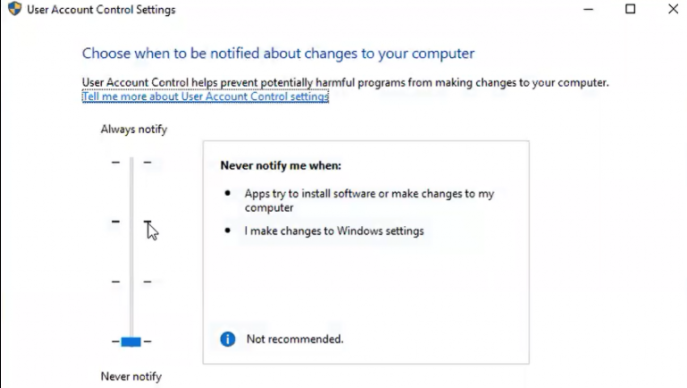
Adjust this setting to the bottom-most position (Never notify), as shown in the above illustration.
- Disable the IPv6 network protocol.
- This control is available in the Windows Network Settings. to navigate to network settings:
Navigate to Control Panel > Network and Internet > Ethernet.
From the Ethernet screen, click Change adapter options. A new screen opens that displays one or more networks.
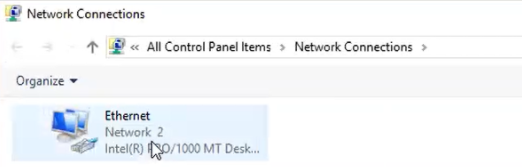
Right click the network on which to disable IPv6, and click Properties from the popup menu.
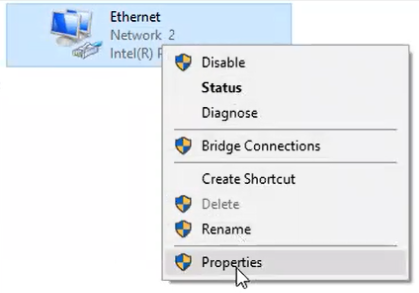
The Ethernet Properties screen appears.
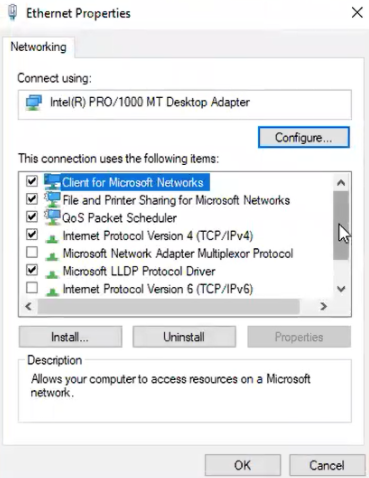
Scroll down to the Internet Protocol Version 6 (TCP/IPv6) setting, and ensure that it is unselected or disabled.
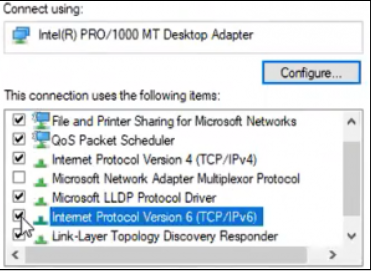
Click OK to save changes. The system returns you to the Ethernet page of Control Panel.
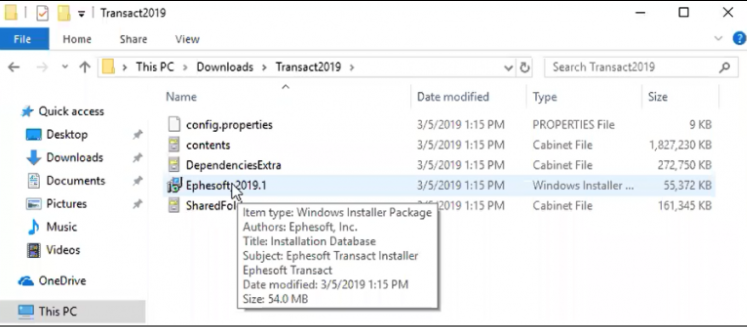
Once you extract the zipped Install Wizard package, you can view the contents of the Install Wizard by opening the Transact2019 folder, as shown below:
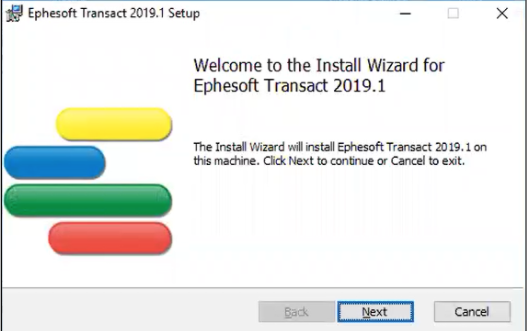
Complete the Install Wizard
The Install Wizard displays the Welcome screen:
Licensing information
- User setup
- Database setup
- Additional parameters as prompted
- Click Next on the Welcome screen. The End-User License Agreement is displayed.
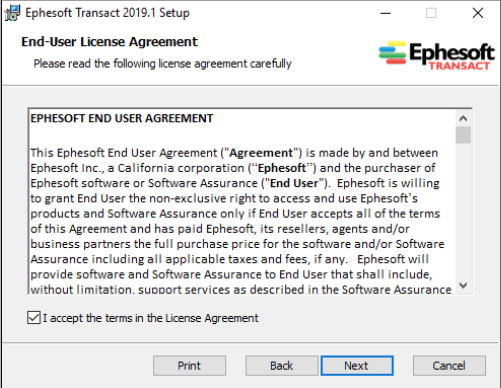
2. Read the terms of the license agreement and click Next to continue.
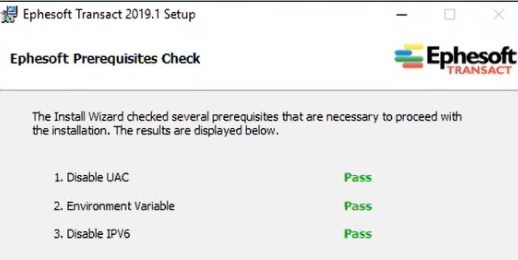
3. Click Next when the prerequisite check is acceptable.
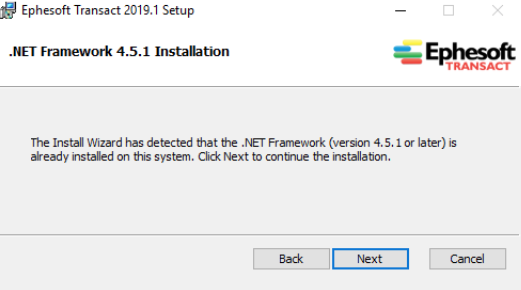
Transact performs a check to verify that the .NET Framework 4.5.1 is installed.
4. Click Next to continue. Transact performs a check of Microsoft® Visual C++ Redistributables.
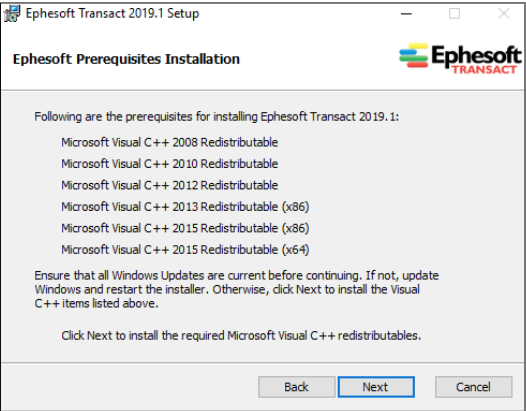
- 1. Microsoft Visual C++ 2010 Redistributable — Download or Download SP1
- 2. Microsoft Visual C++ 2012 Redistributable — Download or Download Update 4
- 3. Microsoft Visual C++ 2013 Redistributable (x86 version) — Download
- 4. Microsoft Hotfix KB2919355 — Download
- 5. Microsoft Visual C++ 2015 Redistributable (x64 version) — Download
- 6. Microsoft Visual C++ 2015 Redistributable (x86 version) — Download
- 7. Microsoft .Net Framework 4.5.1 — Download
- 8. Microsoft® Windows OS should be updated to the latest version — Download options
- 9. Microsoft® SQL Server® 2012 Native Client – QFE* (Version 11.4.7001.0) — Download
- 10. Microsoft® ODBC Driver 13.1 for SQL Server® – Windows, Linux, & macOS (Version 13.1.4413.46) — Download
- 11. Microsoft® Command Line Utilities 13.1 for SQL Server® – Windows, Linux, & MacOS (Version 13.811.168) — Download
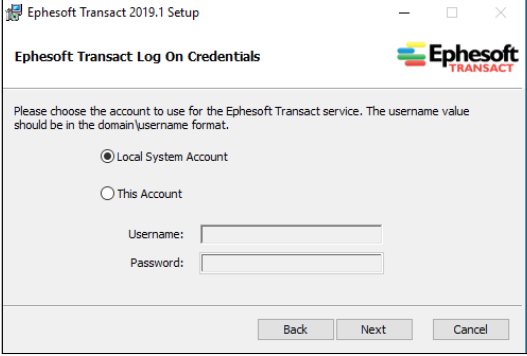
5. Click Next when prerequisites are verified. The Install Wizard prompts you for account selection and log on credentials. In most cases, users select Local System Account.
6. Select the database to install or configure. Click Next.
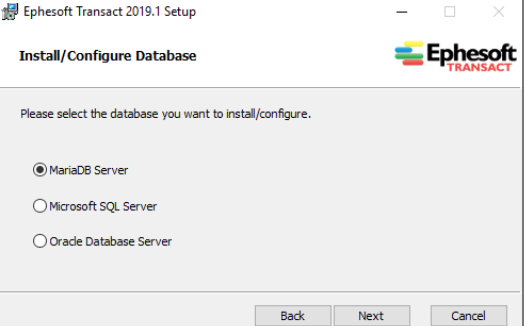
7. Follow these steps when setting up a Maria DB database during the installation of Ephesoft Transact. There are two options for the MariaDB Server setup:
- Install a new instance
- Configure an existing instance
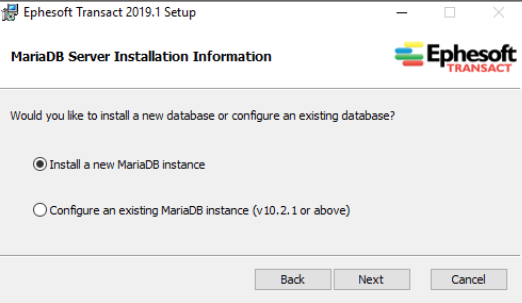
- Select one option for MariaDB and click Next.
- If installing a new MariaDB instance, the following screen appears. Enter the information as prompted.
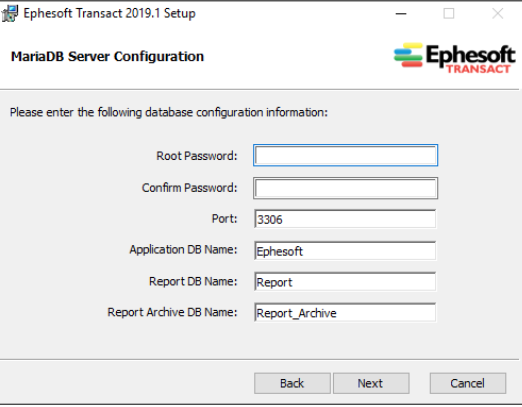
Once you have provided MariaDB server configuration, click Next.
After completing database, the Open Office screen appears.
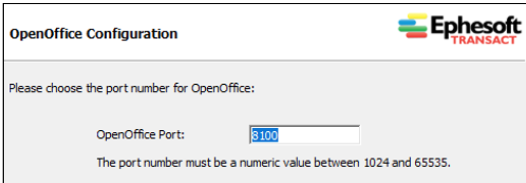
8. Use the default port number, unless the network requires a different port. Click Next to proceed.
The Authentication Mode dialog appears, as illustrated below:
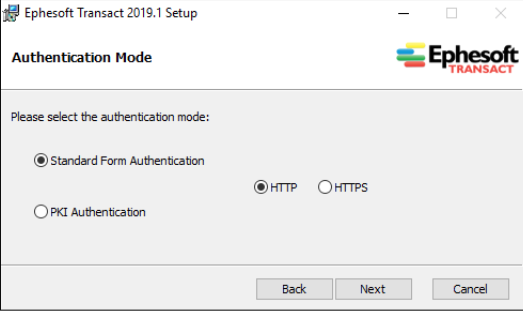
9. Select the appropriate Authentication Mode for this installation of Ephesoft Transact.
Click Next. The following screen appears.
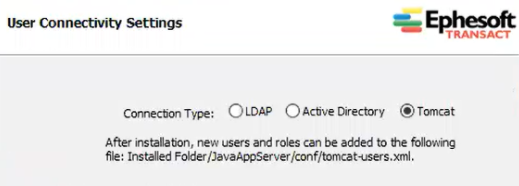
Tomcat — The following snapshot illustrates the first screen of User Connectivity Settings for Tomcat. If this applies to the installation, click Next.
Once you have completed User Connectivity Settings with the previous step, the Ephesoft Registration Information screen appears.
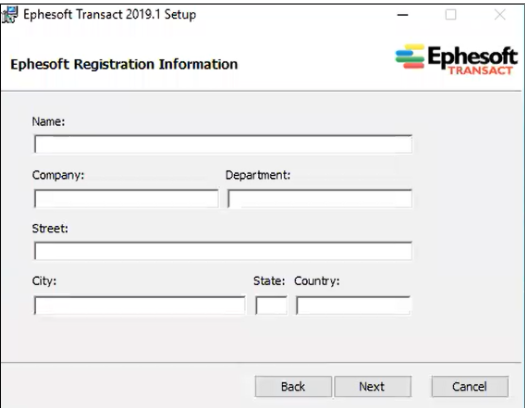
10. Enter the appropriate information in the text fields and click Next. The Shared Folder Configuration screen appears.
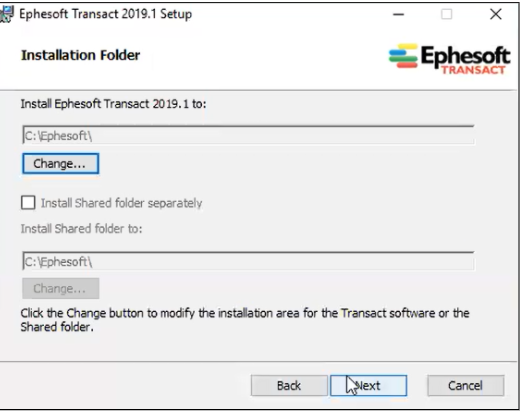
Click Next. The Installation Folder screen appears.
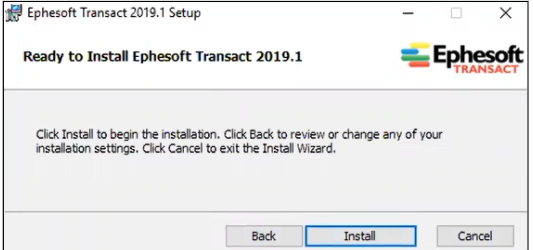
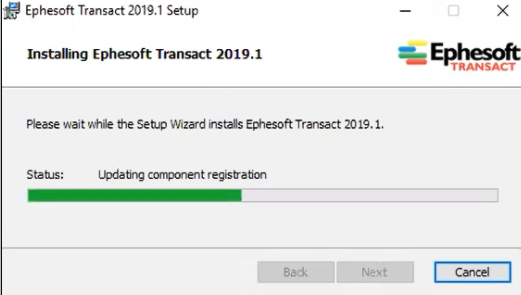
Click Install to launch the installation process. A Status bar displays progress of the installation.
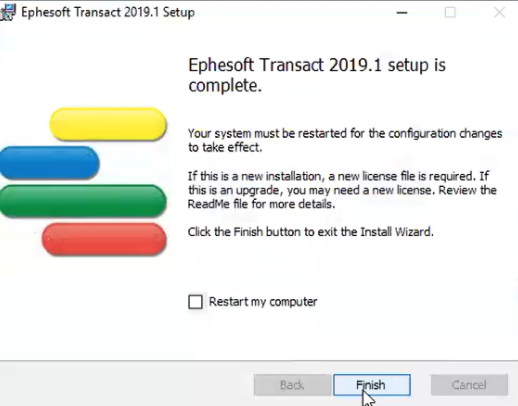
Once the Install Wizard has completed the installation, it provides Post-Installation Instructions.
Click Finish to complete the installation, without restarting the computer.
License and Launch Ephesoft Transact 2019.1
Licensing and launching Ephesoft Transact after installation must include these general tasks:
- Install the Ephesoft license
- Enable the Ephesoft Transact service on Windows
- Launch the Ephesoft Transact application, to view the home page and log in
Obtain and install the license for Ephesoft Transact with instructions provided in the following document:
• Licensing Ephesoft Transact 2019.1
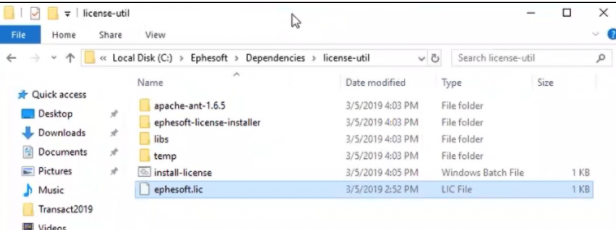
The target location of the license file is typically as follows:
— {Ephesoft directory}\Dependencies\license-util\
The following snapshot illustrates the typical location for the license:
Double click on install-license
Start the Ephesoft Transact service
a. In the Windows start menu, or the Windows Control Panel, search for Services | Desktop App.
b. Right click the Services utility and run as administrator. The Services (Local) screen appears. Scroll down to EphesoftTransact.
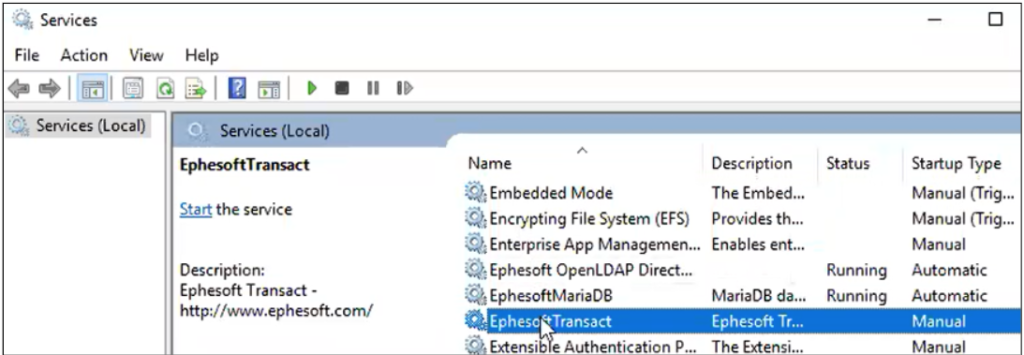
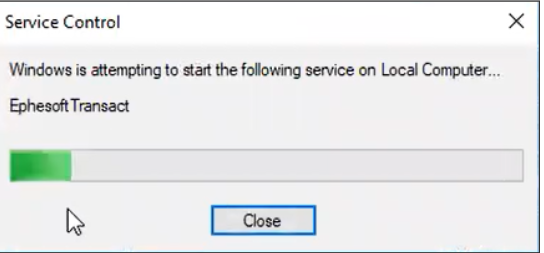
c. If the EphesoftTransact service is not running, right click EphesoftTransact, and click Start. The service starts with the following progress indicator:
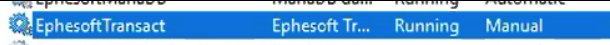
Upon successful startup of the EphesoftTransact service, the status will display Running.
Launch Ephesoft Transact. Follow these steps:
a. Launch a Web browser session.
b. Enter the location of the Ephesoft Transact application. The following URL illustrates the typical path when running Ephesoft Transact on the local system: https://localhost:8080/dcma/home.html
Select Administrator or Operator to log in.
Enter the Username and Password.
Ephesoft with ADFS over SAML 2.0 with Authentication Type 2
Create self-signed certificates with OpenSSL
Here you can download Open SSL & Perl
Locate OpenSSL CA.pl file as this file is required to create dummy CA certificate file. This will be inside the bin directory within the OpenSSL directory
Create a directory where you want to create new certificates. Execute the following command from this directory (You might need to edit the OpenSSL path accordingly)
perl C:\OpenSSL-Win32\bin\CA.pl -newca
This creates demoCA/cacert.pem (CA Certificate) and demoCA/private/cakey.pem (private key)
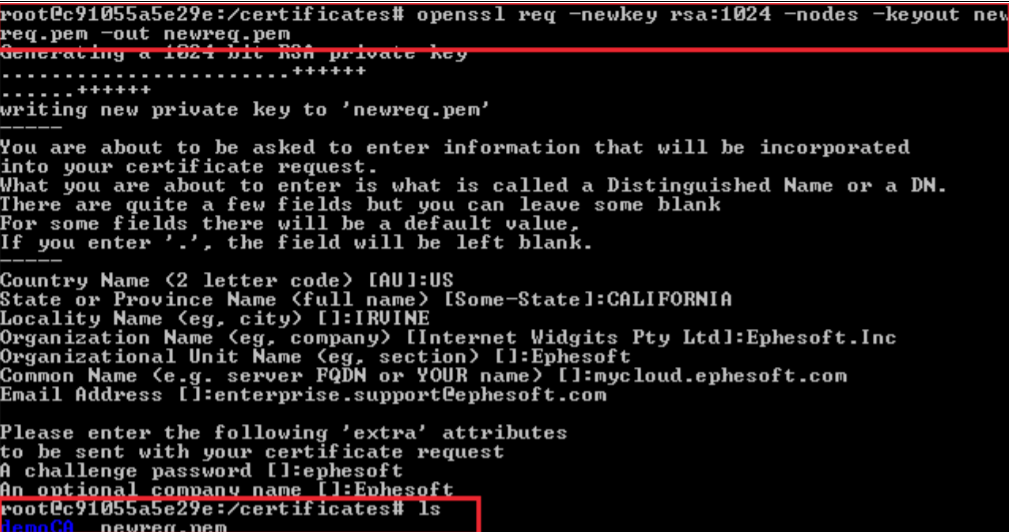
Make a server certificate signing request (CSR) using the following command:
openssl req -newkey rsa:2048 -nodes -keyout newreq.pem -out newreq.pem
Before you run this command you need:
- Country Name (2 letters)
- State or Province Name
- Locality/City Name
- Organization Name
- Organizational Unit Name
- Common Name (servername/hostname) e.g. mycloud.ephesoft.com
- Email Address
Execute the following command (You might need to edit the path accordingly)
perl C:\OpenSSL-Win32\bin\CA.pl -sign
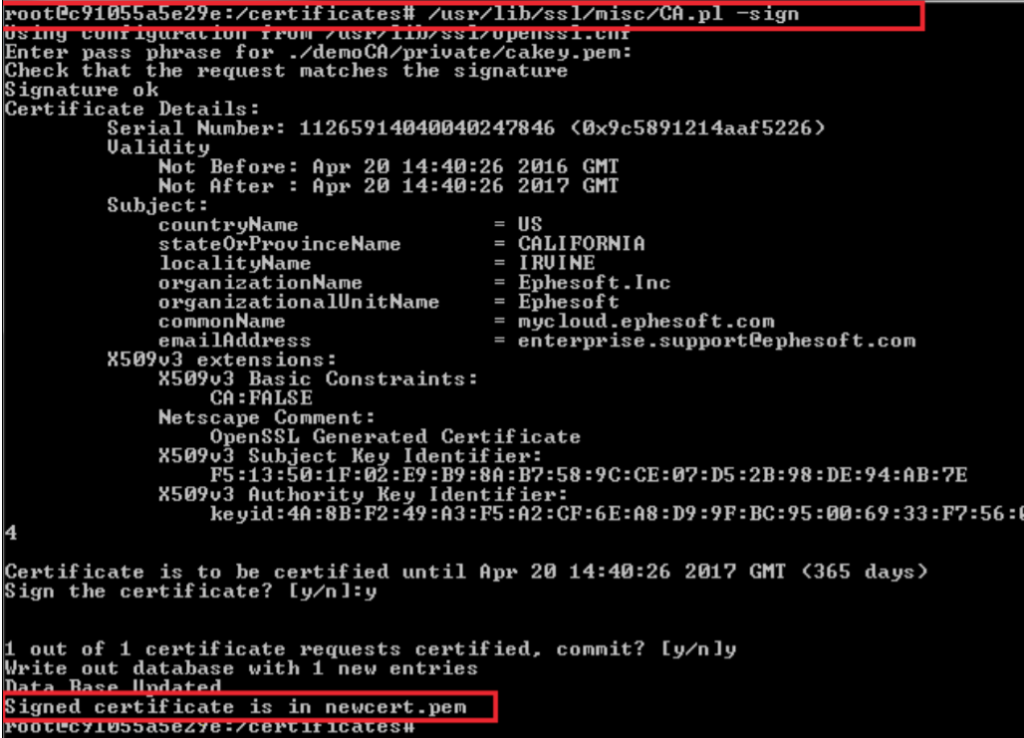
After the above steps have been followed, you will have the 3 following files: cacert.pem, newreq.pem and newcert.pem.
Rename newreq.pem to serverkey.pem and newcert.pem to servercert.pem.
Convert the servercert.pem file to PKC12 format (*.p12) using the following command:
openssl pkcs12 -export -in servercert.pem -inkey serverkey.pem -out servercert.p12 -name servercertificate
Create a java keystore file by converting the servercert.p12 file to Java Keytool format by using the following command:
keytool -importkeystore -destkeystore servercert.jks -srckeystore servercert.p12 -srcstoretype PKCS12 -alias servercertificate
Navigate to the demoCA directory (cd demoCA) and create a java truststore file by converting the cacert.pem file to Java Keytool format by using the following command:
keytool -import -keystore cacert.jks -alias cacert -file cacert.pem
Configuring the Ephesoft Transact JavaAppServer (Tomcat)
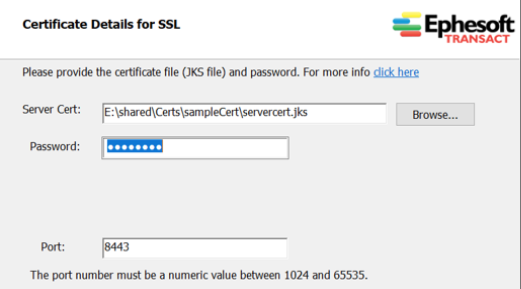
To configure the Tomcat Connector using CA/Self-Signed Keystore and Truststore certificates, perform the following steps:
- Make a backup copy of the existing web.xml file located in the <Ephesoft>/JavaAppServer/conf folder.
- Open web.xml in edit mode, and locate the existing HTTP/HTTPS connector, as shown in the snapshot.
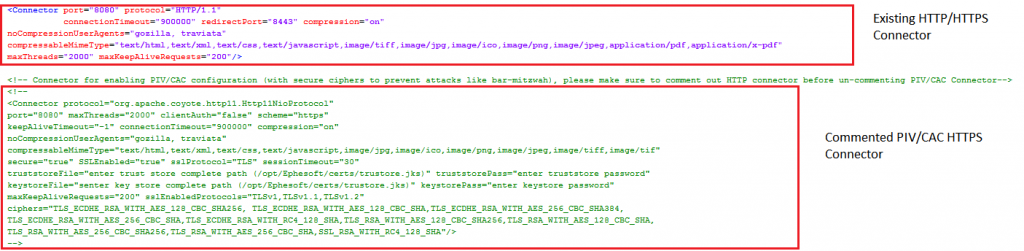
Comment the existing connector (default port 8080) and create a new connector by manually adding the following properties in the server.xml file:
| protocol: | org.apache.coyote.http11.Http11NioProtocol |
| port: | 8443 (change port number if required) |
| maxThreads: | 2000 |
| clientAuth: | false |
| scheme: | https |
| keepAliveTimeout: | -1 |
| connectionTimeout: | 900000 |
| secure: | true |
| SSLEnabled: | true |
| sslProtocol: | TLS |
| sessionTimeout: | 30 |
| truststoreFile: | (truststore file generated previously) |
| truststorePass: | <password for trustore> |
| keystoreFile: | (keystore files generated previously) |
| keystorePass: | <password for keystore> |
| maxKeepAliveRequests: | 200 |
Example
<Connector protocol="org.apache.coyote.http11.Http11NioProtocol" port="8443" maxThreads="2000" clientAuth="false" scheme="https" keepAliveTimeout="-1" connectionTimeout="900000" compression="on" noCompressionUserAgents="gozilla, traviata" compressableMimeType="text/html,text/xml,text/css,text/javascript,image/jpg,image/ico,image/png,image/jpeg,image/tiff,image/tif" secure="true" SSLEnabled="true" sslProtocol="TLS" sessionTimeout="30" truststoreFile="enter trust store complete path" truststorePass="enter truststore password" keystoreFile="enter key store complete path" keystorePass="enter keystore password" maxKeepAliveRequests="200" maxPostSize="4194304" />
The following files need to be configured in cases where you are setting up Ephesoft Transact files for SSL/TLS:
- EPHESOFT_HOME/Application\WEB-INF\classes\META-INF\dcma-batch\dcma-batch.properties
- EPHESOFT_HOME/Application\WEB-INF\classes\META-INF\dcma-workflows\dcma-workflows.properties
- EPHESOFT_HOME/Application/WEB-INF/xml
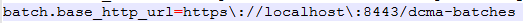
dcma-batch.properties
Modify the base_http_url to include the https protocol, correct port and hostname.
dcma-workflows.properties
Modify the wb.hostURL to include the https protocol, correct port and correct host.

web.xml
- Make a backup copy of the existing web.xml file.
- Modify the following <context-param> entries:
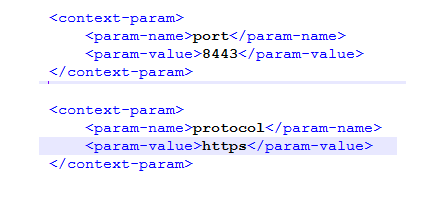
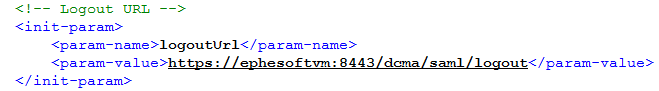
- The Logout URL needs to be of the following format:
https://{hostname}:{port-number}/dcma/saml/logout
Configurations for Integrating SAML-Enabled Spring Security Framework
The following files need to be configured:
- EPHESOFT_HOME/Application/xml
- EPHESOFT_HOME/Application/WEB-INF/xml
- EPHESOFT_HOME/application/WEB-INF/classes/security/jks
- EPHESOFT_HOME/Application/WEB-INF/classes/META-INF/applicationContext-security.xml
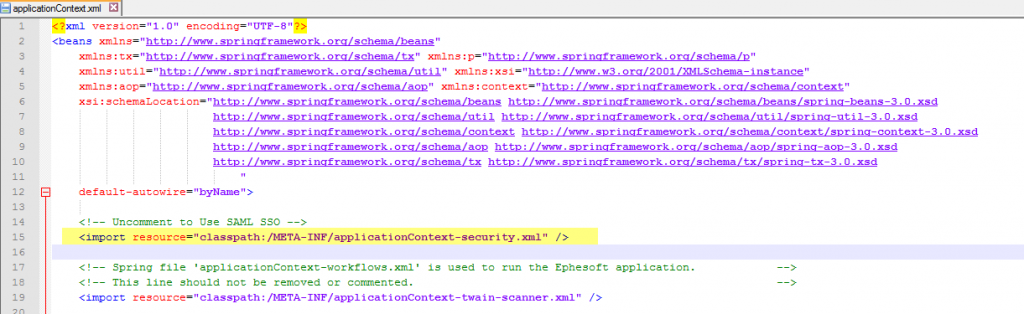
applicationContext.xml
Uncomment the applicationContext-security.xml resource in applicationContext.xml to use SAML SSO.
web.xml
- Uncomment the springSecurityFilterChain and its filter mapping.
- Comment out the following elements in the web.xml file:
- SessionTimeoutFilter and its filter mapping
- SessionTimeoutServlet and its filter mapping
- All security-constraints and login-config nodes
- The session-config node needs to be commented out in the xml file.
- Configure the logout URL according to the server details.
- The logout URL needs to follow this form: https://{hostname}:port/dcma/saml/logout
- The authenticationFilter and its mapping must be prior in sequence to the authorizationFilter in the filter chain.
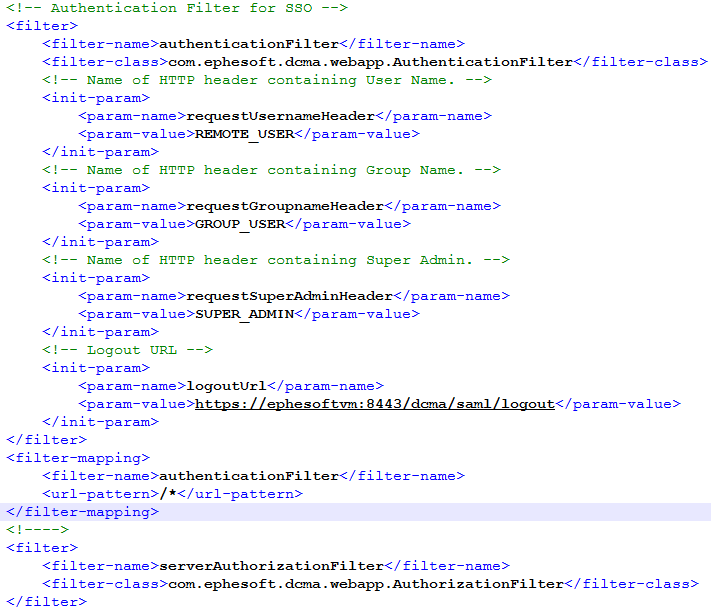
- Select the appropriate value for authenticationType as per the following logic:
- If only the username will be passed along as attribute in the SAML message, and authorization will be determined by Ephesoft Transact.
- If the username, group and isSuperAdmin values will be passed along as attributes in the SAML message.
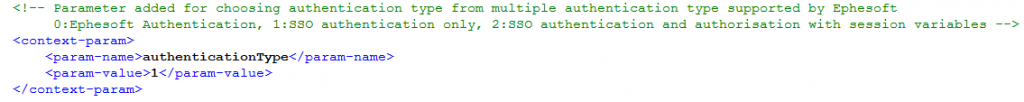
If authenticationType=1 (i.e. Authentication Only), roles need to be defined as per the property defined in user-connectivity.properties (<Ephesoft_Installation_directory>\Application\WEB-INF\classes\META-INF\dcma-user-connectivity\user-connectivity.properties). The user.connection property defines where the roles will be mapped.
If user.connection=0, roles for the user will be mapped in LDAP user.connection=1, roles for the user will be mapped in AD user.connection=2, roles for the user will be mapped in tomcat-users.xml(<Ephesoft_Installation_directory>\JavaAppServer\conf\tomcat-users.xml)
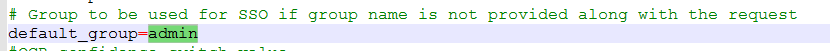
If authenticationType=2 (i.e. Authentication and Authorization are done by IdP) and the group is not received from ADFS server, then, by default the system will use the group defined in default_group property of application.properties (<Ephesoft_Installation_directory>\Application\WEB-INF\classes\META-INF\application.properties).
Multiple Group Support in web.xml
By default, when using SSO, Ephesoft Transact presumes that every user will be associated with a single group. To enable a single user with multiple groups for authentication Type = 2, certain configuration changes are required.
Follow the steps in the following Ephesoft Wiki article to make such configurations for multiple groups.
samlKeystore.jks
A Java Keystore (JKS) is a repository of security certificates. SAML exchanges involve usage of cryptography for signing and encryption of data. This keystore will contain a certificate and private key that will be used to digitally sign the SAML messages and to encrypt their content.
A default keystore with the name samlKeystore.jks is provided in the application. However, the user can also create a custom keystore.
Create a private key
- Open the command prompt at key tool path and run the following command for generating the private key for customKeystore.
C:\Program Files\Java\jdk1.7.XXXX\bin>keytool.exe -genkeypair -alias “alias for private key” -keypass “password for key” -keystore “path to keystore”
- Enter “nalle123”.
- Complete the following prompts as applied to your organization.
After confirming all the added information, the private key will be added to the keystore.
- Place this newly created customKeystore.jks file at the following location:
“EPHESOFT_HOME/application/WEB-INF/classes/security/”
- Update the applicationContext-security.xml file as described below.
Note: Ephesoft recommends that you record separately the alias for the private key created and corresponding password. These are required for an upcoming task.
applicationContext-security.xml
In the bean “epheSamlFilter”, update the value of the constructor argument which you have added in IdP, as per the below logic. The third constructor argument must be true for superadmin access, otherwise this must be false. If this is from IdP, a claim name can be passed to indicate whether the user is superadmin or not. That claim name can be specified here.
- Index=0: Path of Username Attribute passed in SAML message.
- Index=1: Path of Group Attribute passed in SAML message.
- Index=2: Path of IsSuperAdmin Attribute passed in SAML message.
<bean id="epheSamlFilter" class="com.ephesoft.dcma.webapp.SamlFilter"> <constructor-arg index="0" value="https://schemas.xmlsoap.org/ws/2005/05/identity/claims/name"/> <constructor-arg index="1" value="https://schemas.microsoft.com/ws/2008/06/identity/claims/role"/> <constructor-arg index="2" value="true"/> </bean>
By default, it is configured as /home.html.
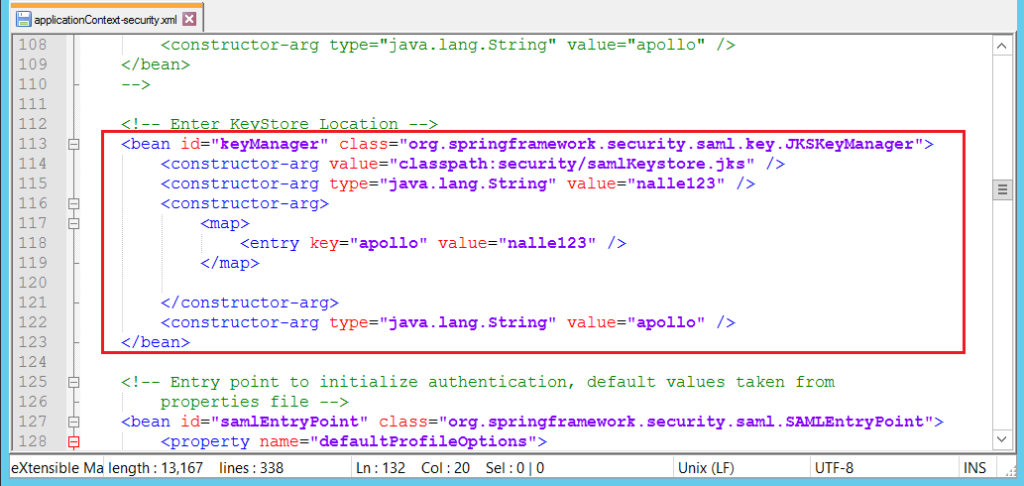
In the bean “keyManager”, the constructor arguments need to be populated according to the following logic:
- First constructor argument: the path of keystore needs to be added here (Default: classpath:security/samlKeystore.jks). If you have created new keystore, specify that keystore.
- Second constructor argument: the password of keystore needs to be added here (Default: nalle123).
- Third constructor argument: the private key and corresponding password created in the previous section need to be added in the map constructor (Default: <entry key=”apollo” value=”nalle123″ />).
- Fourth constructor argument: the private key to be used needs to be provided here (Default: apollo).
To use encryption, you also need to uncomment the following commented bean set in the applicationContext-security.xml file.
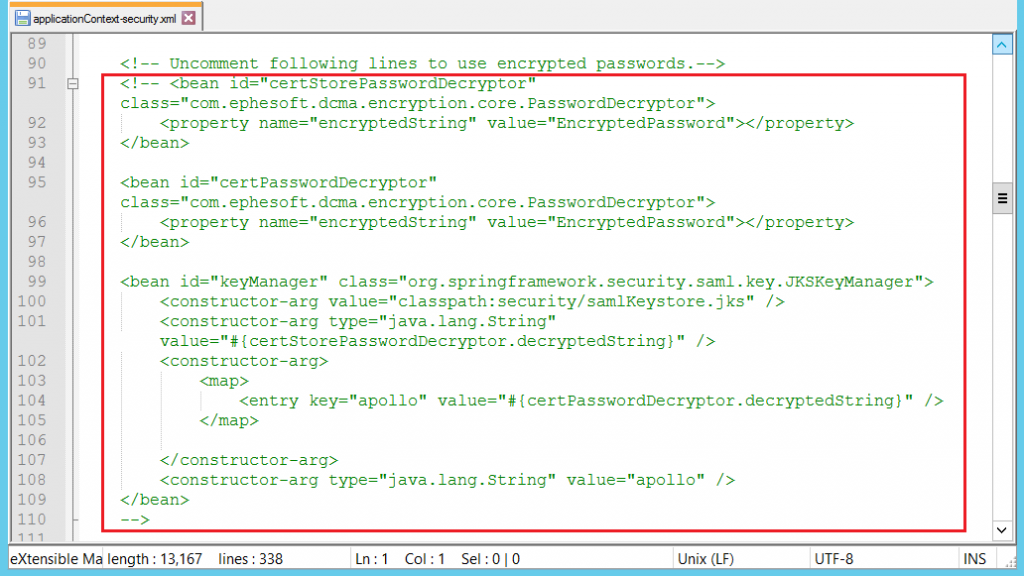
Here, in the beans “certStorePasswordDecryptor” and “certPasswordDecryptor”, replace the string “EncryptedPassword” with your encrypted password value, keeping the quotation marks (example: “nROcbAKcSGR7CsxrlNVZSA==”).
Then, comment out the similar bean “keyManager” right below the above-mentioned lines:
Update the “metadataGeneratorFilter” bean as shown below. Perform these steps to configure the metaGeneratorFilter.
a. This task requires the entityId, which the customer must provide to Ephesoft. The customer security administrator typically provides the entityID.
An entityID is a globally unique name for a SAML entity. Specific requirements for the entityId differ according to the requirements of the specific identity provider.
Update the entityId with the value that pertains to the user’s metadata, which is to be uploaded at the identity provider (IdP).
Update the entityBaseURL with hostname and port number values. This will be the public DNS address, and contains https:// at the beginning and /dcma at the end.
<bean id="metadataGeneratorFilter" class="org.springframework.security.saml.metadata.MetadataGeneratorFilter">
<constructor-arg>
<bean class="org.springframework.security.saml.metadata.MetadataGenerator">
<property name="entityId" value="urn:super:ephesoft:ggn" />
<property name="requestSigned" value="true" />
<property name="entityBaseURL" value="https://{hostname}:{portNumber}/dcma" />
<property name="extendedMetadata">
<bean class="org.springframework.security.saml.metadata.ExtendedMetadata">
<property name="signMetadata" value="true" />
<property name="idpDiscoveryEnabled" value="false" />
</bean>
</property>
</bean>
</constructor-arg>
</bean>
Configure the “metadata” Metadata configuration can be done in one of the following ways:
a. Save IdP metadata in a file and place it in the following folder:
“EPHESOFT_HOME/application/WEB-INF/classes/security”
b. Update the bean as shown below and specify the classpath as “/security/<filename.xml>”.
c. To disable signature verification, set the metadataTrustCheck property to false.
<bean id="metadata" class="org.springframework.security.saml.metadata.CachingMetadataManager"> <constructor-arg> <bean class="org.springframework.security.saml.metadata.ExtendedMetadataDelegate"> <constructor-arg> <bean class="org.opensaml.saml2.metadata.provider.ResourceBackedMetadataProvider"> <constructor-arg> <bean class="java.util.Timer"/> </constructor-arg> <constructor-arg> <bean class="org.opensaml.util.resource.ClasspathResource"> <constructor-arg value="https://www.fellow-consulting.com/security/FederationMetadata.xml"/> </bean> </constructor-arg> <property name="parserPool" ref="parserPool"/> </bean> </constructor-arg> <constructor-arg> <bean class="org.springframework.security.saml.metadata.ExtendedMetadata"> <property name="requireLogoutResponseSigned" value="true"/> </bean> </constructor-arg> <property name="metadataTrustCheck" value="false"/> </bean> </constructor-arg> </bean>
d. Using the IdP metadata URL, modify the “metadata” bean and use ExtendedMetadataDelegate and HttpMetadataProvider as shown below.
Also, define the metadataTrustCheck as false to skip signature validation. Update the metadata URL to the IdP metadata URL that is provided in the following code: https:///FederationMetadata/2007-06/FederationMetadata.xml
<bean id="metadata" class="org.springframework.security.saml.metadata.CachingMetadataManager"> <constructor-arg> <list> <bean class="org.springframework.security.saml.metadata.ExtendedMetadataDelegate"> <constructor-arg> <bean class="org.opensaml.saml2.metadata.provider.HTTPMetadataProvider"> <constructor-arg> <value type="java.lang.String">https://ADFSServer/FederationMetadata/2007-06/FederationMetadata.xml</value> </constructor-arg> <constructor-arg> <!-- Timeout for metadata loading in ms --> <value type="int">5000</value> </constructor-arg> <property name="parserPool" ref="parserPool"/> </bean> </constructor-arg> <constructor-arg> <bean class="org.springframework.security.saml.metadata.ExtendedMetadata"> <property name="requireLogoutResponseSigned" value="true"/> </bean> </constructor-arg> <property name="metadataTrustCheck" value="false"/> </bean> </list> </constructor-arg> </bean>
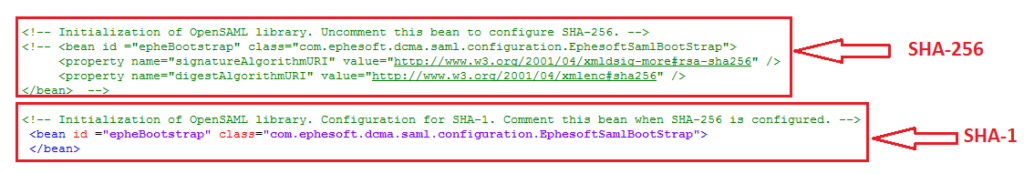
- SHA-256 Support: By default, the application is configured to provide SAML configuration with SHA-1. To configure SHA-256, comment the bean for SHA-1 and uncomment SHA-256 bean.
Testing at the SSOCircle
Perform the following steps to test Ephesoft at the SSOCircle (IdP)
- Create an account at the SSOCircle and log in.
- Add the service provider’s metadata in the SSOCircle.
You can download Ephesoft metadata using the following path:
https://{ephesoft_ip}:{port}/dcma/saml/metadata
The entityID should be the FQDN that is registered at the SSOCircle.
The SSOCircle metadata is available from the following online resource:
https://idp.ssocircle.com/idp-meta.xml
Configuring Ephesoft Transact and ADFS
Configuring Ephesoft Transact for the ADFS Server
Before completing these steps, ensure that the following prerequisites are in place:
Ensure that Ephesoft Transact has already been configured on HTTPS.
Ensure that the Ephesoft Transact server is running prior to downloading metadata.
In the case that a broken page is displayed while downloading Ephesoft metadata, this means that the Ephesoft server did not start correctly.
Resolve any errors that caused a failure by using the following log file:
<Ephesoft_HOME>/Application/logs/dcma-all.log
Follow these steps to configure ADFS settings on Ephesoft Transact:
Obtain the ADFS Metadata
- Download the ADFS metadata from the default URL:
- https://<ADFSServer>/FederationMetadata/2007-06/FederationMetadata.xml
- Copy the downloaded metadata at the following path:
- <Ephesoft_Home>/Application/WEB-INF/classes/security
Import the ADFS Certificates to Ephesoft Transact
To export the certificate from ADFS, view the section Exporting the Certificate from the ADFS Server.
To import ADFS certificates, use the following command:
keytool.exe -importcert -alias adfssigning -keystore samlKeystore.jks -file adfsCertificate.cer
Configuring the ADFS Server for Ephesoft Transact
Follow these steps to set up the ADFS Server for operation with Ephesoft Transact.
- Download the Ephesoft Transact metadata from the following path: https:///dcma/saml/metadata
- Add the Relying Party Trust with the following steps:
a. In ADFS, navigate to the following folder:
AD FS\Trust Relationships
b. Right click the Relying Party Trusts folder under ADFS\Trust Relationships. The following snapshot illustrates this navigation.
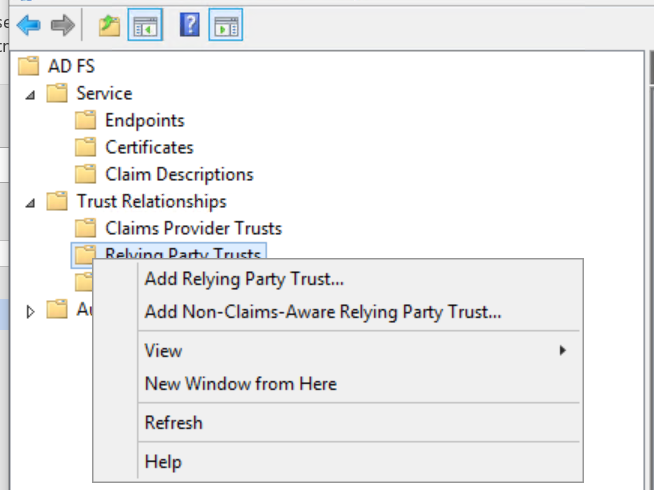
c. From the popup menu, click Add Relying Party Trust…
The Add Relying Party Trust Wizard appears.
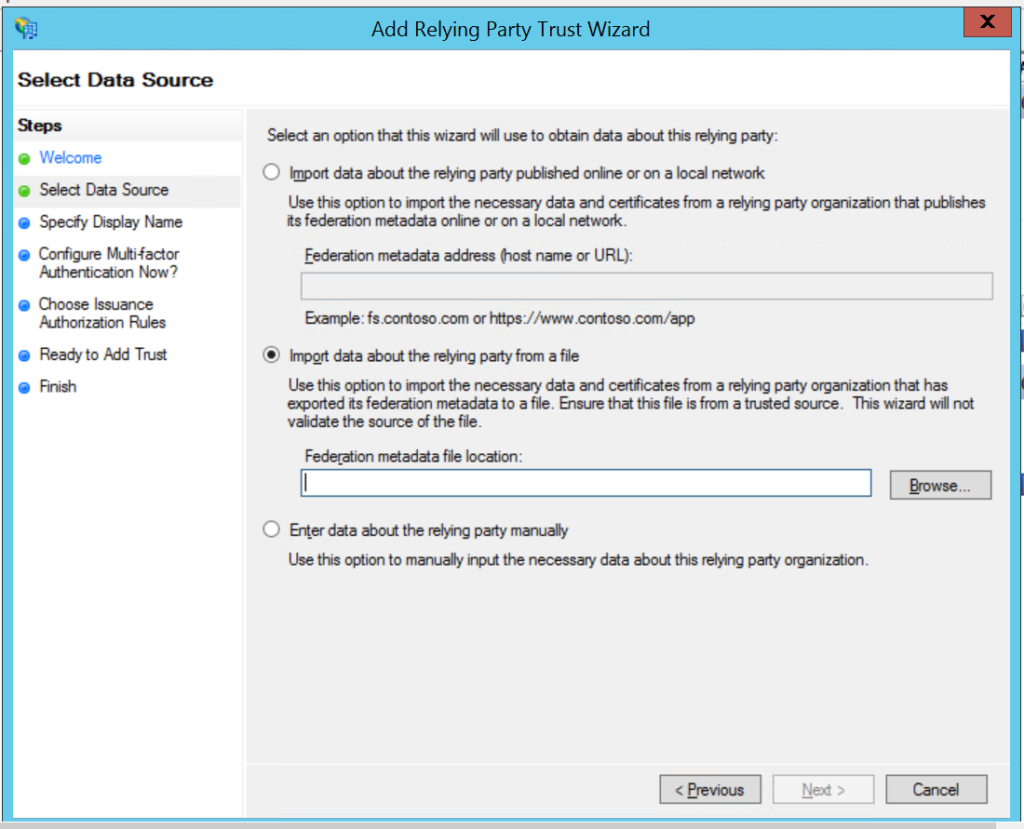
- Choose (select) the Import data about Relying Party from a file option and select the metadata XML file saved in step 1.
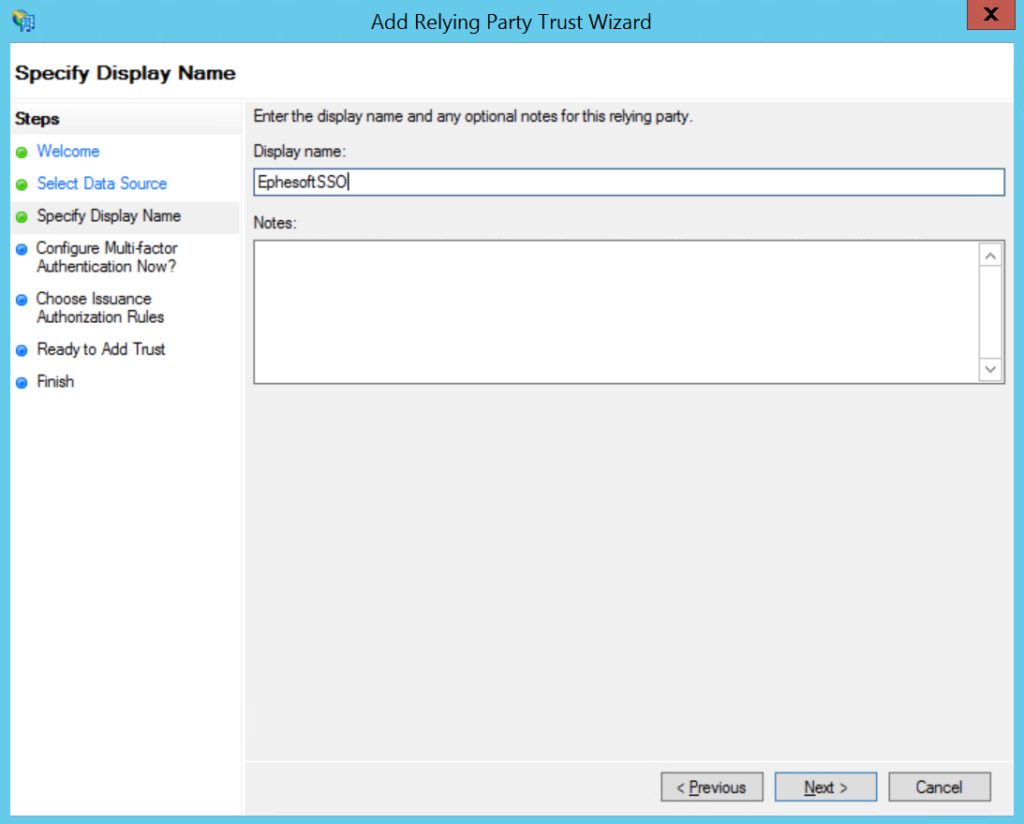
- Provide a display name and click Next by choosing the default setting.
- Add the following claims.
a. NameId: Sends the Name ID.
i. Rule Name: NameId
ii. Choose “SAM-Account-Name” as the LDAP Attribute and “Name ID” as the Outgoing claim type.
b. FirstName: Sends name details.
i. Rule Name: FirstName
ii. Choose “SAM-Account-Name” as the LDAP Attribute and “Name” as Outgoing claim type.
c:[Type == "https://schemas.microsoft.com/ws/2008/06/identity/claims/windowsaccountname", Issuer == "AD AUTHORITY"]
=> add(store = "Active Directory", types = ("https://schemas.microsoft.com/ws/2008/06/identity/claims/role"), query = ";tokenGroups;{0}", param = c.Value);
ii. Filtering Groups — Define a filter to restrict groups sent in claims.
— Select the Pass Through or Filter an Incoming Claim
— Add the Rule Name as Filter Groups.
— In the field, Pass through all claims that start with specific value, specify Enterprise.
The group claim rules need to be configured only if authenticationType=2 is set in the web.xml file.
In the web.xml file, if the authenticationType is 1 (that is — SSO Authentication Only), then Authorization will be handled by Ephesoft Transact.
ADFS just needs to send the username as a claim to Transact.
- Open the Relying Party Trust by double clicking it. In the Advanced tab, change Secure Hash Algorithm to SHA-1/SHA-256, to be as configured in Ephesoft Transact.
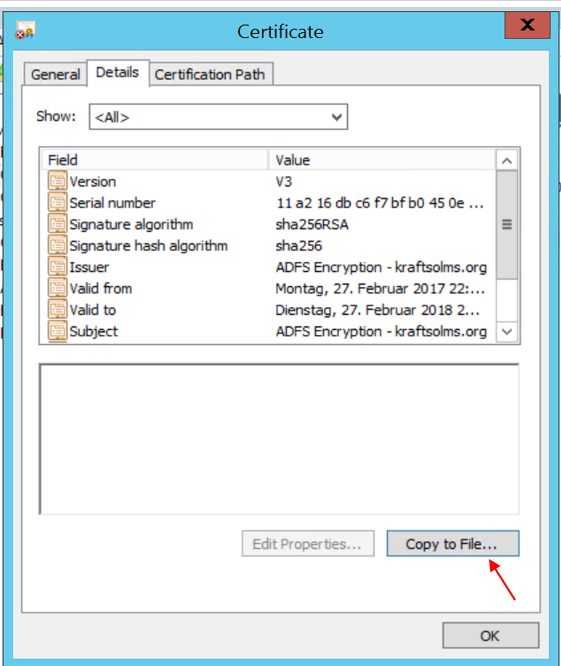
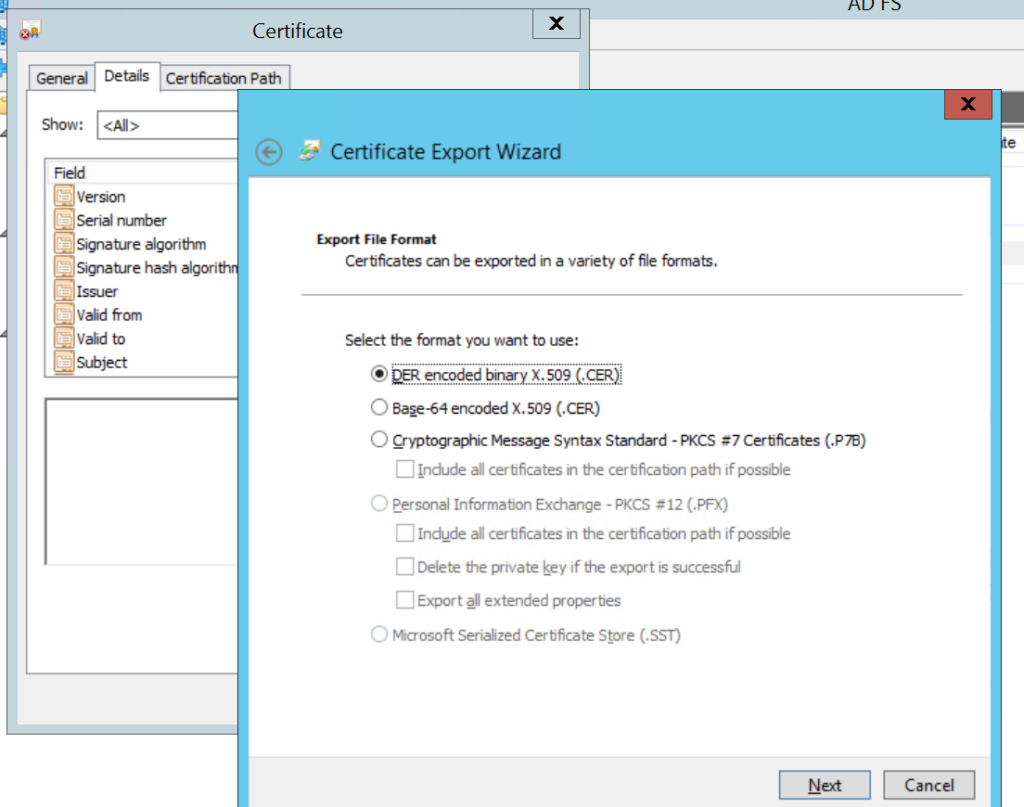
Exporting the Certificate from the ADFS Serve
- In ADFS, select the Certificate option under ADFS/Service.
- Double click the certificate to export. Navigate to the Details tab, click Copy to File and save this as a DER-encoded certificate in your file system.
Note: The exported certificates can be saved to any accessible path on your file system.
This exported certificate from ADFS needs to be imported in samlKeystore.
How configure Infor SSO?
Infor Multi-Tenant Configuration
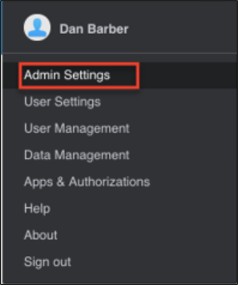
- Select Admin Settings.
- Select Add Application.
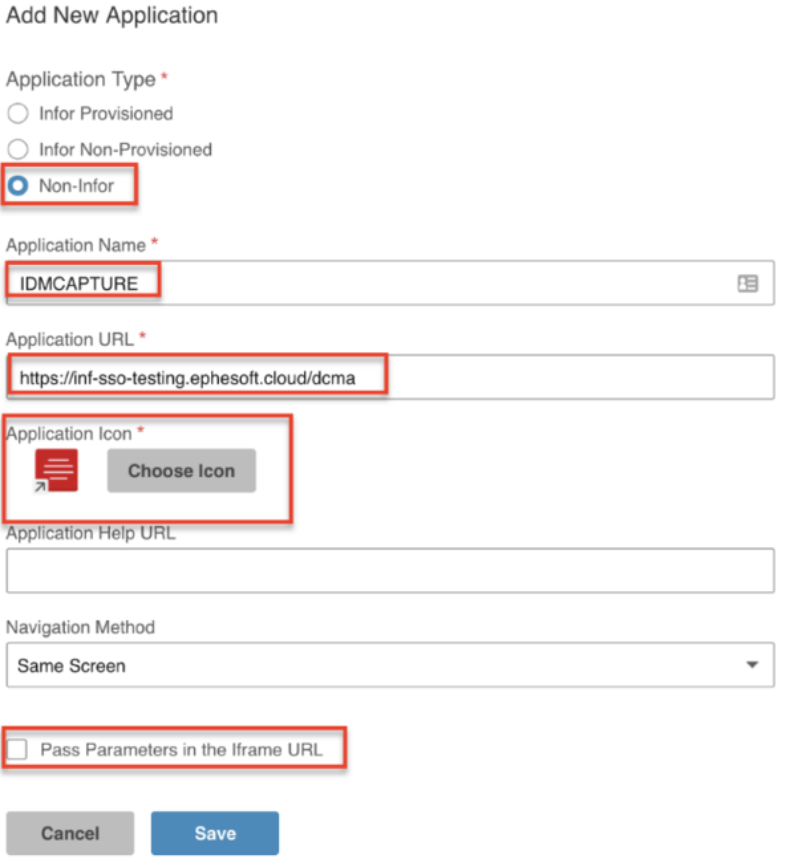
- For Application Type, select Non-Infor.
- For Application Name, enter IDMCAPTURE.
- Refer to the email from the Infor Procurement Team. For Application URL, enter the Ephesoft Transact URL provided.
- Select Choose Icon.
- Select any of the available icons for the Capture application.
- Select color of choice.
- Select Done.
- Unselect Pass Parameters in the frame URL.
- Select Save.
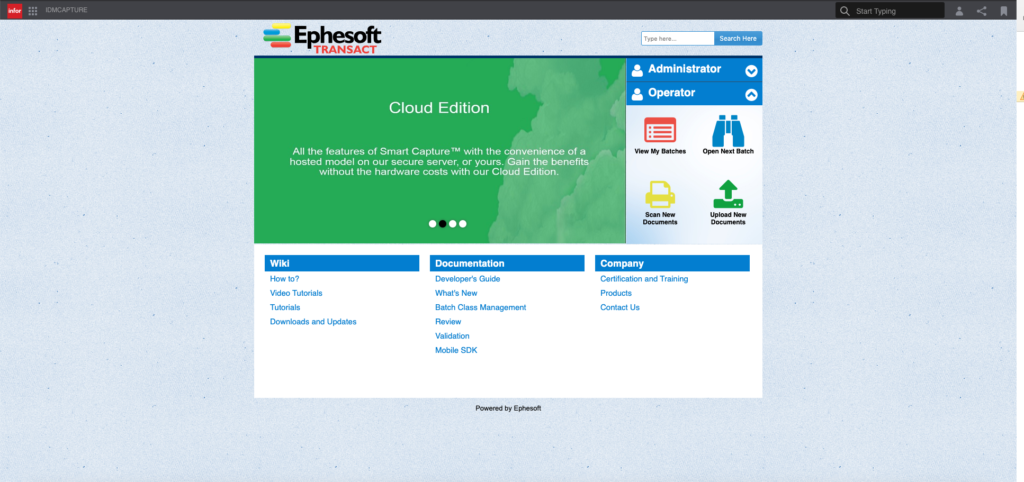
Successful Configuration
When accessing the Ephesoft Transact page, the user will be redirected to the Infor login screen.

About Fellow Consulting
Fellow Consulting AG, based in Poing near Munich, has been advising clients on digitizing their business processes for more than 10 years.
We know how our customers can implement their digital vision.
Together with our partners infor_ Amazon AWS, Microsoft Azure, SugarCRM, and Ephesoft, we bring the mission of digitalization to life.
We act as an operational and strategic specialist for our clients as well as a sparring partner for the everyday challenges of digital transformation.